YOUR CAR
CAN BE STOLEN
in under 60 seconds with no alarm triggered
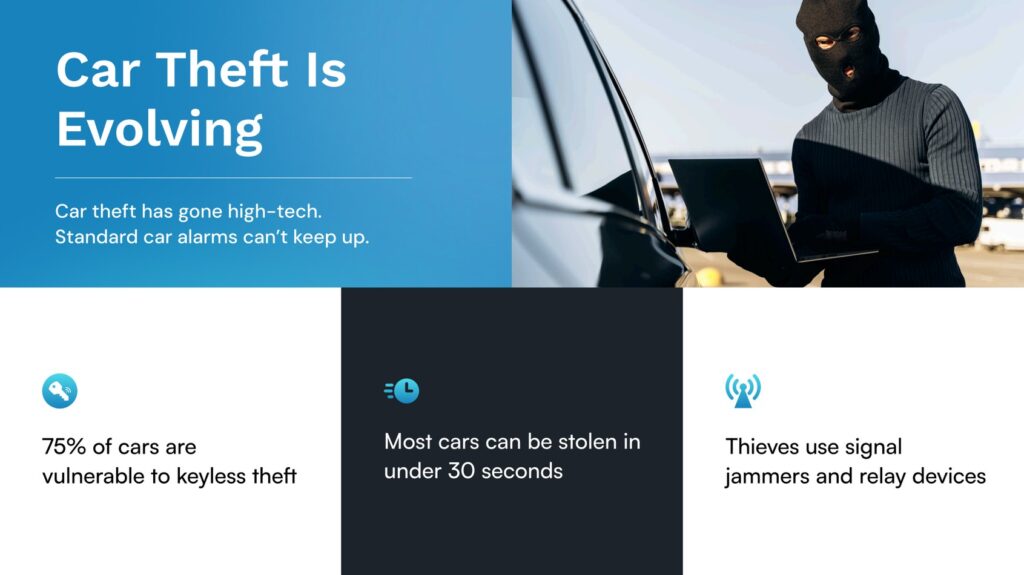
CAN bus attack vs relay attack — what’s the difference?
Two distinct theft methods are driving the surge in keyless vehicle crime across the UK. CAN bus injection and relay amplification both allow criminals to steal modern cars without a key — but they work differently, target different vehicles, and require different defences. LockCar’s hardwired immobiliser stops both.
On this page
When West Midlands Police dismantled a chop shop network in late 2024, they found criminals equipped with both relay amplifiers and OBD programming devices. Modern vehicle theft gangs are not limited to a single technique — they choose the most efficient method for each target. Understanding both CAN bus injection and relay attacks is essential for any UK vehicle owner who wants to make an informed decision about protection. LockCar manufactures anti-theft devices in the UK specifically to defeat both attack vectors at the point that matters most: the engine start circuit.
Relay attack — how it works
A relay attack exploits the passive entry system fitted to every modern keyless vehicle. The car broadcasts a low-power challenge signal continuously. When the genuine key fob is within range — typically around one metre — it responds with an encrypted handshake, and the car unlocks and allows the engine to start. Relay equipment extends this “within range” condition artificially, allowing a criminal standing outside your property to amplify the key fob’s signal from inside your house to the car parked on your driveway.
The attack requires two criminals and two devices: a relay amplifier near the key, and a relay receiver near the vehicle. The total cost of entry-level relay equipment has fallen to under £100 on criminal markets. The attack takes 20 to 60 seconds from approach to the vehicle moving. No windows are broken, no alarms are triggered, and no physical evidence of theft is typically left at the scene.
Relay attacks are most common between 10pm and 4am on residential driveways. The primary targets are Land Rover, BMW, Toyota, Ford, Mercedes, and Jaguar models with push-button start. The West Midlands, Greater Manchester, South Yorkshire, and London account for the highest recorded relay theft volumes in the UK.
CAN bus attack — how it works
A CAN bus attack (also known as OBD port injection or headlight wire injection) takes a different approach. Instead of amplifying the key fob signal, criminals physically access the vehicle’s CAN (Controller Area Network) bus — the internal communications network that connects every electronic component in a modern car.
The most common entry point for a CAN bus attack is the OBD-II diagnostic port, which on most vehicles is located under the dashboard within easy reach. A second method involves breaking into the headlight housing, which provides access to wiring that connects directly to the CAN bus. Criminals insert a specialist device that mimics the signal of a legitimate key fob at the electronic control unit level — bypassing the keyless entry system entirely and commanding the ECU to authorise engine start.
CAN bus attacks are typically faster than relay attacks when physical access is achievable. However, they require the criminal to physically enter the vehicle or access the engine bay or headlight housing, which creates a brief window of exposure that relay attacks avoid entirely. CAN bus equipment capable of performing the attack is widely available online and has been seized in numerous UK police operations targeting organised vehicle theft groups.
West Midlands Police confirmed that CAN bus attacks are rising at some of the fastest rates in the UK across Birmingham B8, B10, B11, B18 and CV postcodes. Criminals are now routinely carrying both relay and CAN bus equipment, selecting the most appropriate method based on the target vehicle and its environment.
Key differences between the two methods
Understanding the operational differences between relay and CAN bus attacks helps clarify why a single-layer defence is insufficient. The two methods have different risk profiles, different vehicle entry requirements, and different countermeasures — but both share one critical requirement: the ability to start the engine. That shared requirement is the point at which LockCar intervenes.
Relay attacks require no physical contact with the vehicle. The criminal never needs to touch the car, force entry, or access any wiring. The vehicle is unlocked and started using the legitimate key signal, making it virtually indistinguishable from normal use. CCTV footage of relay attacks often shows nothing more unusual than two people walking near a parked car before it drives away.
CAN bus attacks require either physical access to the OBD port (inside the vehicle) or access to the headlight wiring. This means criminals must first gain entry to the vehicle — sometimes by smashing a window or using tools to force a door — before executing the attack. The additional step increases exposure time and leaves evidence, but the attack itself still bypasses the factory immobiliser entirely.
Which vehicles are targeted by each method?
Relay attacks are most effective against vehicles with passive keyless entry, particularly those where the key fob remains active and broadcasting even when the vehicle is locked and parked. Land Rover Discovery and Range Rover models, BMW 3 and 5 Series, Toyota RAV4 and Land Cruiser, and Ford Kuga are among the most frequently targeted via relay across the UK.
CAN bus attacks tend to target vehicles where the OBD port is easily accessible and where the CAN bus architecture is well-documented among criminal networks. Ford, Toyota, and Lexus models have historically been targets for OBD-based key programming, where criminals clone a working key rather than simply bypassing the start circuit. This method is particularly prevalent in stolen-to-order operations, where a specific vehicle is targeted because an end buyer has already been arranged.
Some vehicles are vulnerable to both methods. A Range Rover Sport parked on a driveway might be targeted via relay because it avoids any forced entry. The same vehicle at a car park — where the key fob is too far away for effective relay amplification — might be targeted via CAN bus injection through the headlight housing. Professional theft gangs carry equipment for both scenarios.
Why you need protection against both methods
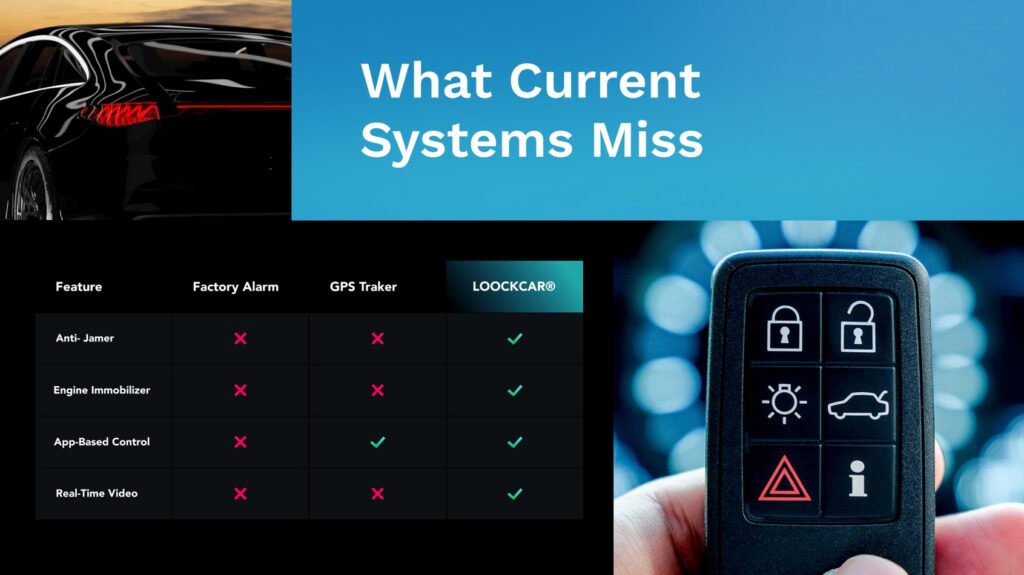
Many aftermarket security products marketed in the UK address only one of these two attack vectors. OBD port locks prevent CAN bus attacks via the diagnostic port but do nothing to stop relay amplification. Faraday pouches block the key fob signal at rest but offer no protection against CAN bus attacks, and no protection during the moments when the key is on your person. GPS trackers provide post-theft data but prevent neither attack.
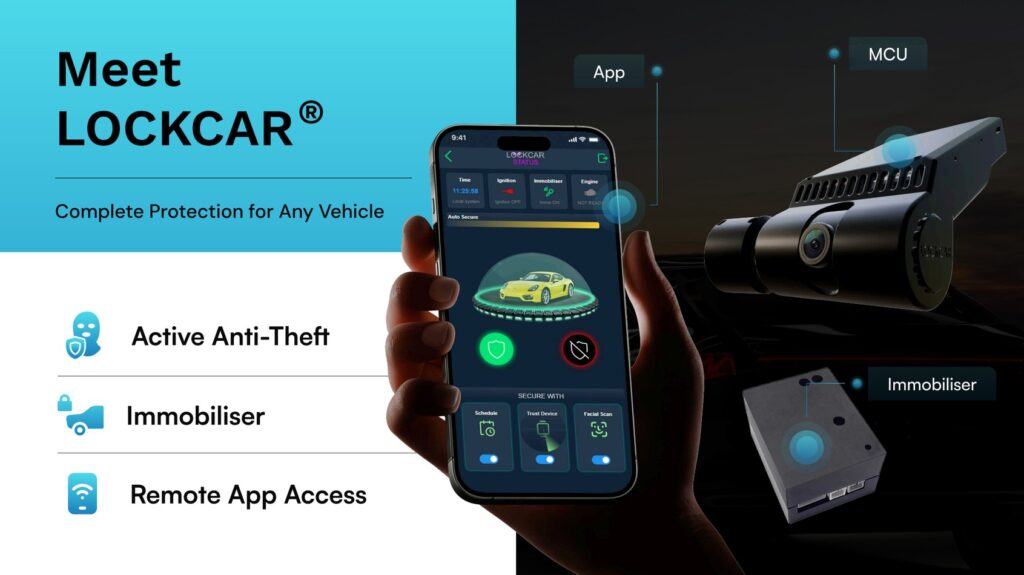
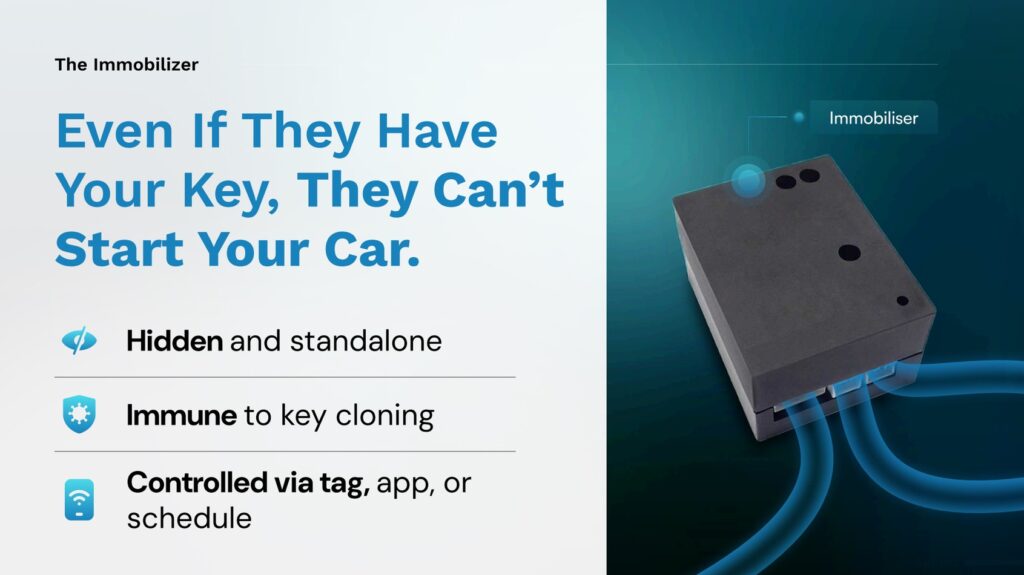
The only defence that stops both relay attacks and CAN bus attacks is one that operates independently of the key fob signal and the OBD port — a physical break in the engine start circuit that requires its own separate authentication before the engine can start. This is precisely the architecture LockCar uses across its entire immobiliser range.
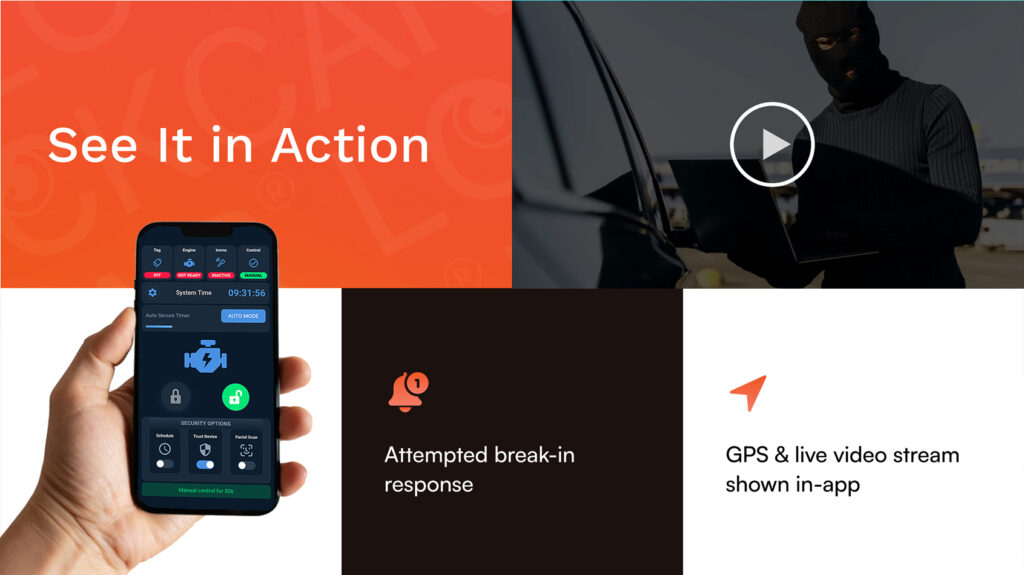
How LockCar defeats CAN bus and relay attacks
LockCar devices install a hardwired relay break in the vehicle’s start circuit. This break is positioned downstream of both the OBD port and the keyless entry system. Even if a criminal successfully performs a relay attack and unlocks the car, or executes a CAN bus injection and commands the ECU to authorise start, the engine will not start because the LockCar relay is open and preventing current from reaching the starter circuit.
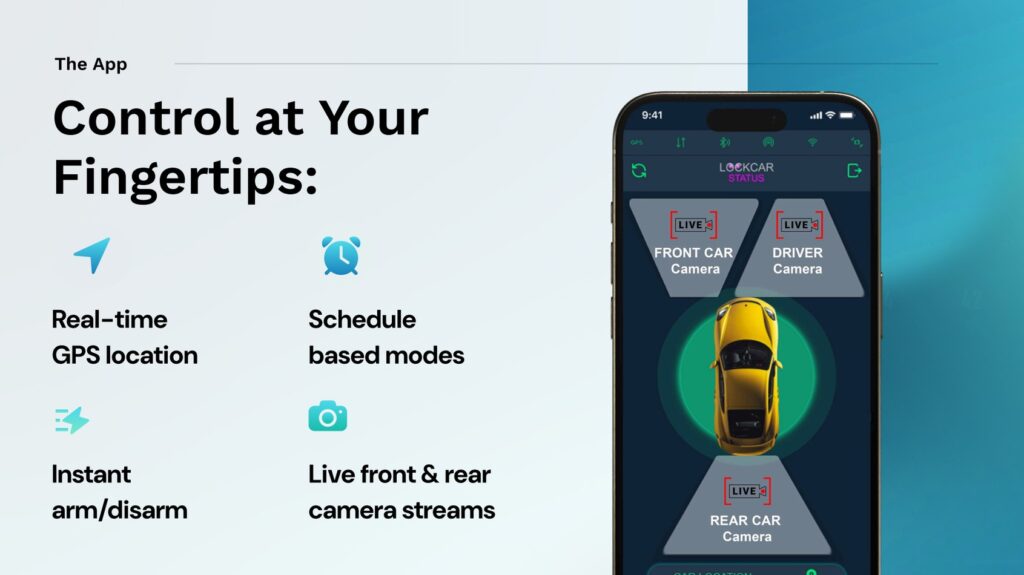
The LockCar relay closes only when a second, independent authentication event is completed. This authentication uses encrypted signals — either a 2.4GHz AES-128 Wi-Fi signal from a proximity tag, a confirmed mobile app interaction, or both — that operate on frequencies and protocols entirely separate from the CAN bus and the keyless entry system. No relay amplifier and no OBD device can generate or replicate these signals.
LockCar systems are manufactured in the United Kingdom. The isolated wiring architecture used in the i226 and i226-based systems adds a further layer of protection: even if a criminal identifies the immobiliser unit and attempts to bridge the relay break directly, the isolated communication channel between the MCU and the immobiliser detects the interruption and maintains the open state. This makes physical bypass attacks against the LockCar unit itself extremely difficult without specialist knowledge of the specific installation.
LockCar immobiliser range
Can an OBD port lock stop a CAN bus attack completely?
An OBD port lock prevents access to the diagnostic port but does not stop CAN bus attacks via alternative entry points such as headlight wiring. LockCar’s hardwired relay break operates downstream of the entire CAN bus, making it immune to attacks from any entry point on the vehicle’s network.
My car already has a Thatcham-approved alarm — am I protected?
Thatcham Category 1 alarms provide detection and notification but do not physically prevent the engine from starting if the factory immobiliser is bypassed. Relay and CAN bus attacks bypass the factory immobiliser entirely, so the alarm may not activate at all. LockCar adds a physical start circuit break that works regardless of whether the alarm or OEM immobiliser is satisfied.
How does LockCar’s isolated wiring architecture improve security?
In a standard wired immobiliser, the communication between the control unit and the relay uses the vehicle’s existing wiring, which a skilled criminal can potentially bridge. LockCar’s isolated architecture uses dedicated, separate wiring between the MCU and the immobiliser module — wiring that carries an encrypted signal. Interrupting this signal maintains the relay in its open, blocking state rather than bypassing it.
Is LockCar suitable for vehicles targeted specifically by CAN bus attacks, like Toyota and Ford?
Yes. LockCar is compatible with all vehicle makes and models including Toyota, Ford, Land Rover, BMW, Mercedes, Nissan, and Lexus. The immobiliser integrates with the start circuit at a point that is independent of the make-specific CAN bus architecture, making it equally effective across all platforms.
Book your LockCar installation
Mobile installation · All vehicles · UK-wide · Same-day available
WhatsApp to book → Call VictorUK-wide