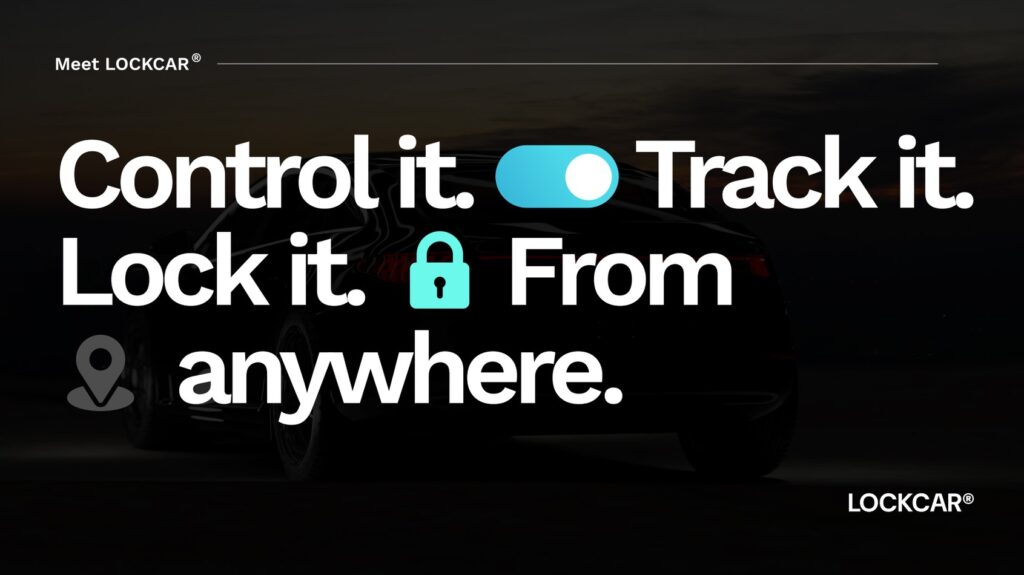
YOUR CAR
CAN BE STOLEN
in under 60 seconds with no alarm triggered
How relay attack steals keyless cars and the physical defence that stops it
Relay attack is responsible for the majority of high-value vehicle theft in the UK. It exploits the keyless entry system that every modern premium car uses. Understanding exactly how it works, and why a physical relay break is the only reliable countermeasure, takes less than five minutes to read.
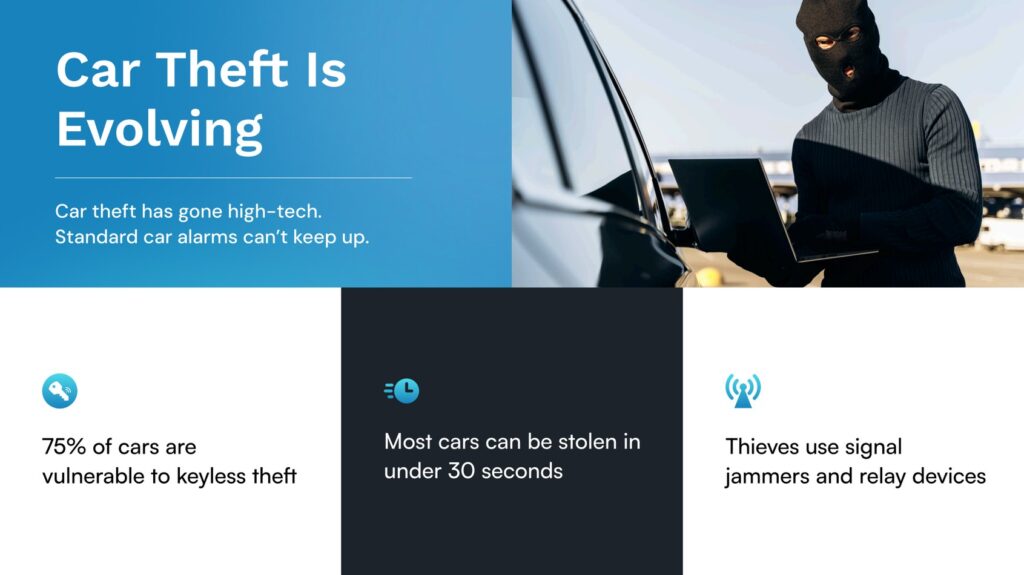
How keyless car theft works in the UK right now
Relay attack is the dominant method of keyless vehicle theft in the UK. It exploits a fundamental vulnerability in passive keyless entry systems, the technology that lets you unlock and start your car without pressing any button on the key fob.
A passive keyless entry system works by continuously broadcasting a low-power radio signal from the vehicle. When the key fob comes within approximately one metre, it detects this signal and responds with an encrypted code. The vehicle verifies the code and permits unlocking and starting.
Relay attack defeats this proximity requirement using two devices: a relay amplifier held near the property where the key is kept, and a relay receiver held near the vehicle on the driveway. The amplifier detects the vehicle’s broadcast signal, amplifies it, and transmits it wirelessly to the receiver. The receiver re-broadcasts the amplified signal, causing the key fob to respond as if it were next to the car. The vehicle accepts the response, unlocks, and permits starting.
West Midlands Police recorded 5,413 stolen vehicles in 2024, the highest of any UK region. The overwhelming majority involved relay attack or OBD key programming on keyless vehicles. Land Rover, BMW, Toyota, and Range Rover models top every theft list because they combine high value with relay-vulnerable passive keyless entry.
Clean infographic showing: house with key fob inside, relay amplifier near door, wireless signal to relay receiver on driveway, vehicle unlocking. Dark background, cyan and orange signal paths.
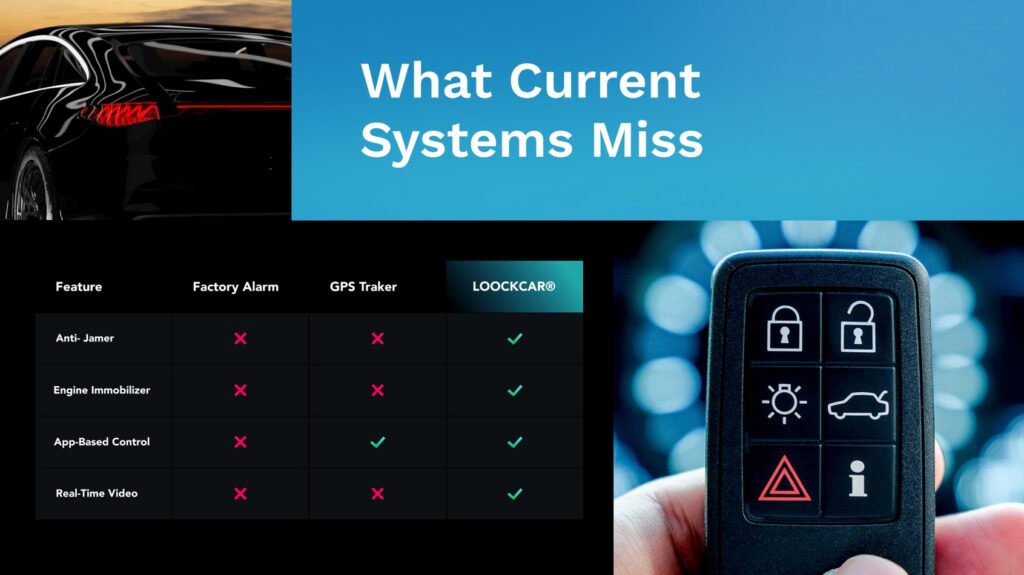
What factory security cannot stop on its own
Every vehicle manufactured since 2000 has a factory immobiliser as standard. In theory, requiring the key to broadcast the correct encrypted transponder code before the ECU permits starting should stop anyone without the correct key.
The problem is that relay attack does not replicate or clone the key. It extends the actual key’s signal from inside the house to the vehicle on the driveway. The factory immobiliser receives what it believes is a legitimate, proximate key signal because it is, in fact, the legitimate key signal, just extended across a longer distance than intended. The immobiliser cannot distinguish between a key that is genuinely one metre away and a key that is twenty metres away with relay equipment extending its reach.
Visual showing two columns: ‘Factory security only’ with relay attack succeeding, and ‘Factory plus LockCar’ with relay attack blocked by the independent relay break. Dark background, cyan for LockCar layer.
Factory Immobiliser
Validates the key transponder signal. Satisfied by relay attack because it cannot distinguish genuine proximity from relay-extended proximity.
OBD Key Programming
Criminals access the OBD port via headlight wiring and use key programming tools to add a new key. Bypasses the factory immobiliser entirely.
CAN Bus Injection
Advanced attacks send commands directly to the vehicle ECU over the CAN bus to unlock doors and permit starting. Not dependent on the key fob at all.
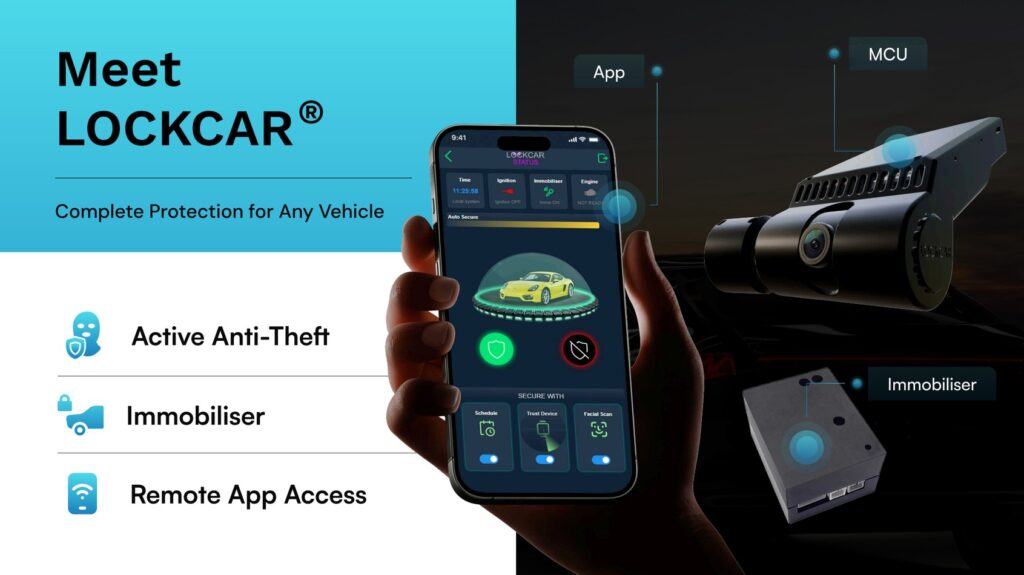
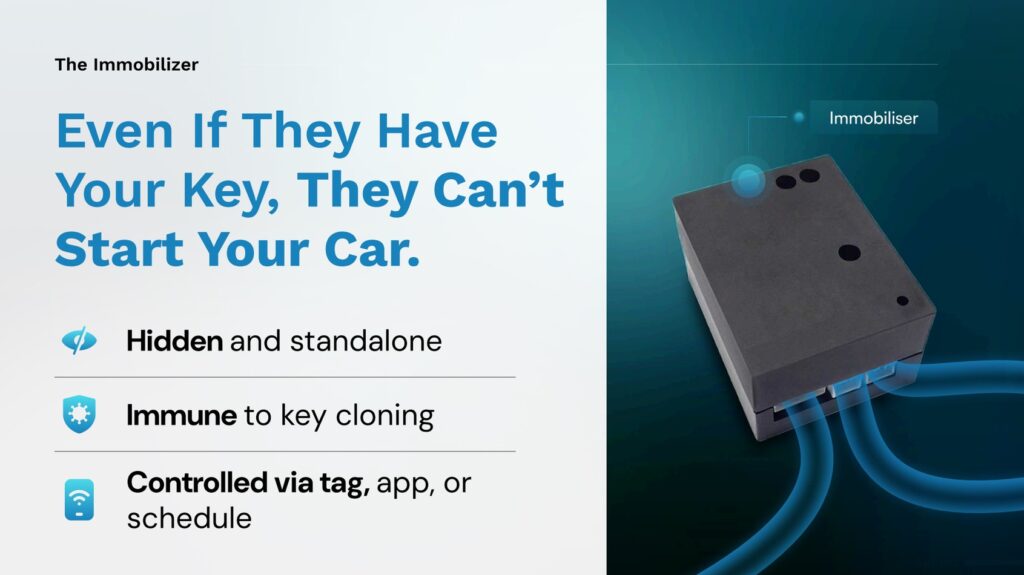
A physical relay break that relay attacks cannot defeat
LockCar addresses relay attack by adding an independent physical relay break in the start circuit that is completely outside the vehicle’s CAN bus, OBD port reach, and factory immobiliser system. This relay break is open by default. Closing it requires an authenticated signal from the LockCar proximity tag or the LockCar app.
The authenticated signal uses AES-128 encryption on a dedicated channel specific to the individual device. It cannot be replicated by relay equipment, which operates on the vehicle’s key fob frequencies. Even if a relay attack perfectly satisfies every factory security check and the ECU is ready to permit starting, the engine cannot start because the LockCar relay remains open.
This is a hardware solution to a hardware vulnerability. Relay attack is fundamentally an RF range extension attack. The LockCar relay break operates on a completely different principle, requiring a specific encrypted credential. The attack has no mechanism to interact with or influence the LockCar relay.
Technical photo showing the LockCar relay unit connected into vehicle wiring. Close-up, professional, shows small form factor and clean installation. Alternatively, a circuit diagram showing relay position after OBD port and CAN bus.
The relay break is downstream of every factory security system and every known attack vector. Even a successful relay attack, a successful OBD key programming, or a successful CAN bus injection leaves the LockCar relay open. The vehicle cannot start.
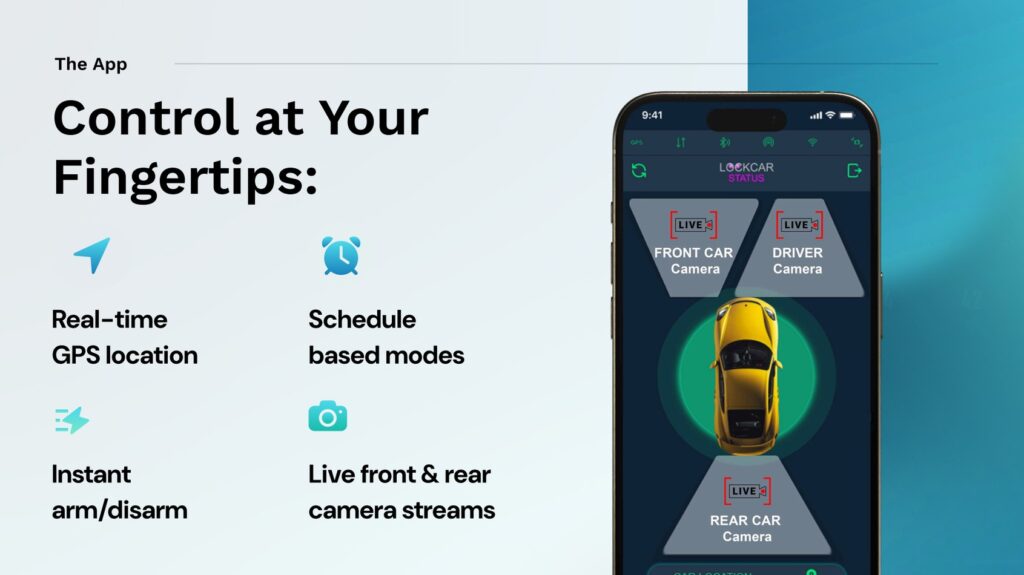
LockCar recommended for this page
Professional product photography of LockCar IC3ST on dark background.
- Hardwired 20A relay break in start circuit
- AES-128 encrypted proximity tag
- Independent of CAN bus and factory system
- Hands-free, auto-disarms as you approach
- No subscription required
- Full insurance certificate provided
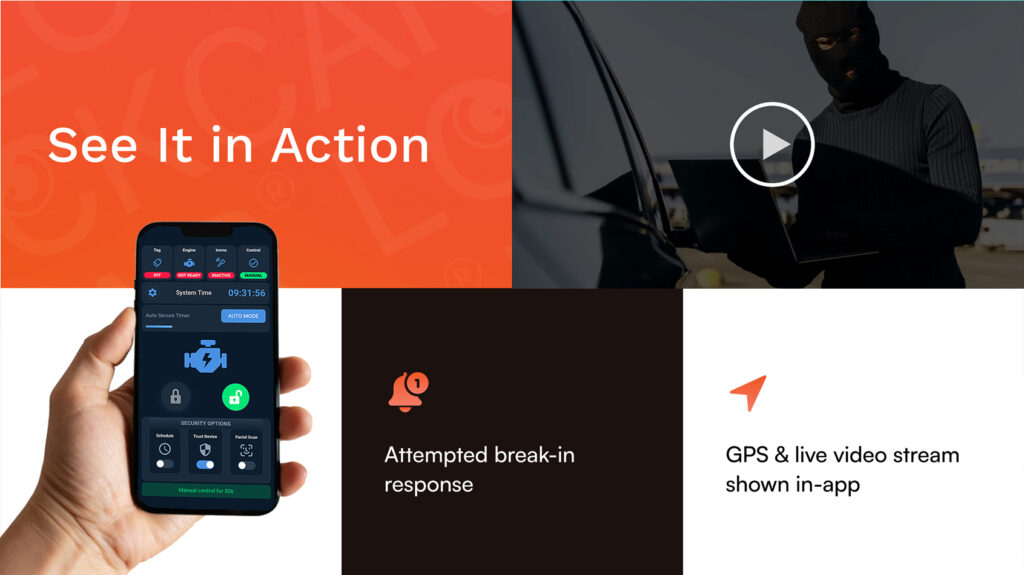
- Relay immobiliser plus 4G GPS tracking
- Live camera stream and movement alerts
- Remote immobilisation from anywhere
- 20A commercial-grade relay
- 12V and 24V support
- Anti-hijack mode included
Frequently asked questions
Does putting my key in a Faraday pouch stop relay attack?
A Faraday pouch blocks the key fob signal when the key is inside the pouch. It provides effective protection for keys stored at home. It provides zero protection in car parks or any situation where the key is on your person. Relay attack in car parks occurs when the key is in the owner’s pocket, not in a pouch.
Will LockCar affect my vehicle warranty?
LockCar installation does not affect your vehicle manufacturer warranty. The installation uses vehicle-specific procedures that avoid any modification to factory electronics. No warranty-relevant components are altered.
Does LockCar work on electric vehicles?
Yes. LockCar’s EV-adapted installation integrates with the drive authorisation circuit rather than a conventional ignition circuit, providing equivalent physical protection for EV platforms including Tesla, BMW i-series, Kia EV6, Hyundai Ioniq, and VW ID series.
How quickly can a relay attack be completed?
A relay attack can be completed in under 60 seconds from approach to the vehicle moving. This is why standard alarm systems and visible deterrents have limited effectiveness against organised relay gangs, who complete the attack before any response can be effective.
Atmospheric photo of a Range Rover or BMW on a residential driveway in the evening. Premium, relevant, conveys the overnight theft scenario without being alarming.
Protect your vehicle from relay attack today
LockCar’s relay break is the only countermeasure that physically stops the engine from starting. Professional mobile installation at your location.