YOUR CAR
CAN BE STOLEN
in under 60 seconds with no alarm triggered
Can Thieves Bypass the Ghost Immobiliser?
Understanding immobiliser vulnerabilities and how LockCar provides robust physical protection.
On this page
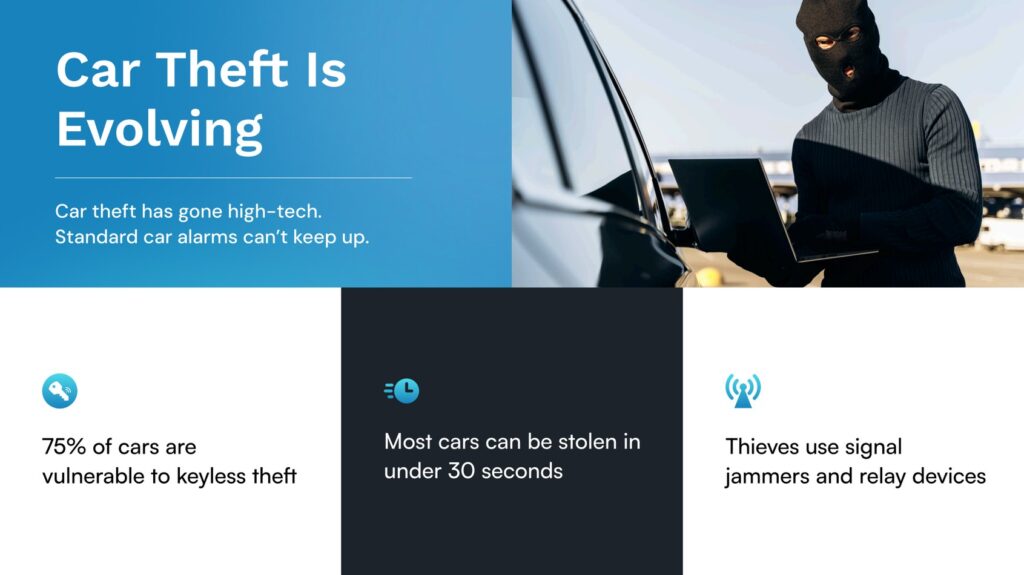
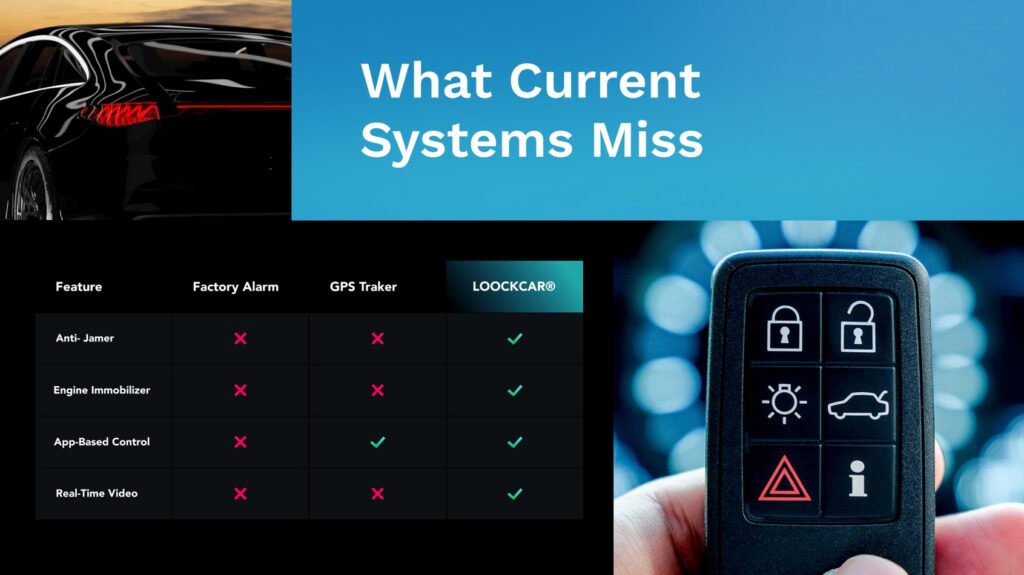
Ghost immobilisers (and similar PIN-code systems) have been popular for several years. They require the driver to enter a code using existing steering wheel or dashboard buttons before starting the engine. But as thieves develop new techniques — particularly CAN bus injection attacks — no immobiliser is completely invulnerable. LockCar’s relay-based immobilisers use a different approach: a physical break in a critical circuit that cannot be bypassed electronically.
How Ghost immobilisers work — and their limits
A Ghost immobiliser intercepts the vehicle’s CAN bus (the communication network that connects all electronic modules). It blocks the start signal until a correct PIN code is entered via steering wheel buttons. The advantage: no additional key fobs or tags to carry. The vulnerability: CAN injection attacks. Thieves with physical access to the OBD port (or certain wiring looms) can inject their own CAN messages to override the immobiliser. Ghost systems are also vulnerable to “ECU swapping” — replacing the vehicle’s engine control unit with a pre-programmed unit that ignores the immobiliser. These attacks require skill and time, but organised theft rings have demonstrated them.
No immobiliser is 100% unbypassable. The goal is to increase the time and skill required to defeat it — most thieves will move to an easier target. LockCar’s relay systems add a physical barrier that electronic attacks cannot cross.
CAN injection attacks and OBD vulnerabilities
Modern vehicles rely on the CAN bus for everything from engine start to window control. Thieves can purchase CAN injector devices online for a few hundred pounds. These devices plug into the OBD port or are wired into exposed CAN wires (often accessible via headlight wiring). The injector sends a “start” command that the vehicle’s ECU accepts as genuine. A CAN-based immobiliser (like Ghost) can be bypassed if the thief knows the correct CAN message to send. LockCar’s relay immobilisers, by contrast, physically cut a circuit. No amount of electronic messaging can close a physical relay that has been opened.
LockCar relay immobiliser range
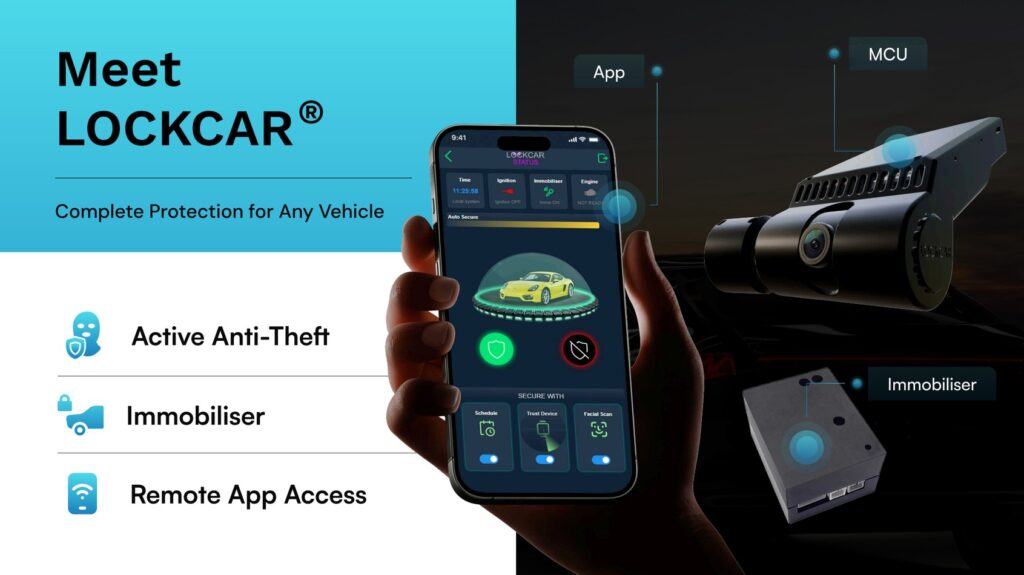
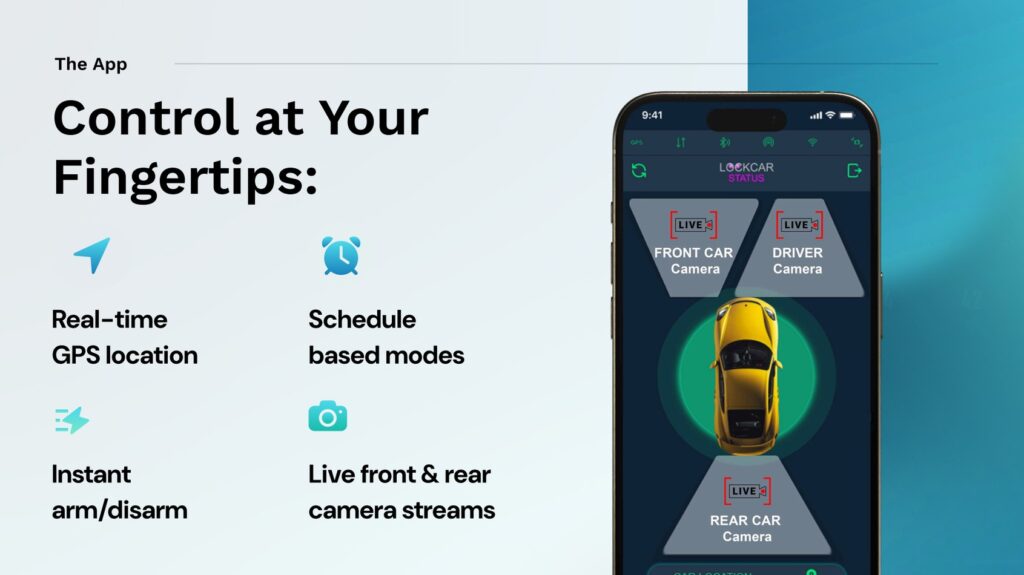
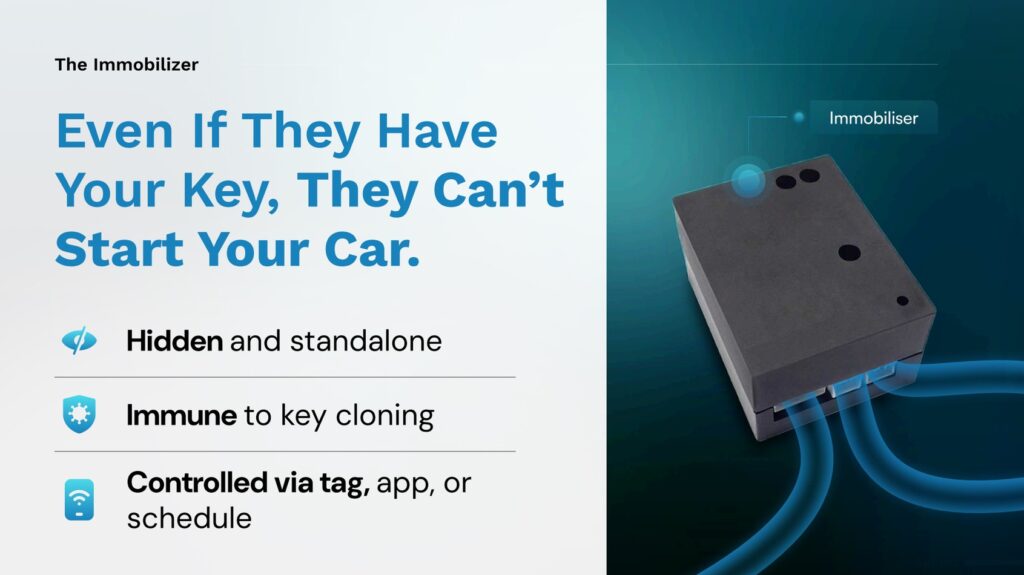
Why LockCar’s relay approach is different
LockCar immobilisers use a physical relay to cut a critical circuit — typically the starter, fuel pump, or ignition. The relay is controlled by a separate LockCar MCU that requires encrypted authentication (Wi-Fi signal, proximity tag, or app authorisation) to close the circuit. A thief using a CAN injector cannot command the LockCar MCU to close the relay because the MCU does not accept CAN bus commands — it has its own encrypted communication protocol. This design eliminates the primary vulnerability of CAN-based immobilisers.
Can a thief bypass a LockCar immobiliser by cutting wires?
Professional installation hides wiring and places the relay in inaccessible locations. Even if a thief finds the relay, they would need to bypass it — which requires identifying which circuit is cut and installing a jumper. This takes significant time, which most thieves won’t risk.
Is Ghost worse than LockCar?
Both have strengths. Ghost’s PIN entry is convenient (no extra fob). But Ghost is vulnerable to CAN injection. LockCar’s relay design is not vulnerable to CAN attacks, but requires carrying a tag or phone. Choose based on your risk profile.
Book your professional installation
Mobile fitting · All vehicles · 12/24V support
WhatsApp to book → Call Victori226 immobiliser