YOUR CAR
CAN BE STOLEN
in under 60 seconds with no alarm triggered
Electric vehicle theft UK — are EVs actually safe?
The rapid growth of electric vehicle ownership in the UK has introduced a new frontier for vehicle theft. EVs are not immune to relay attack — in fact, many EV platforms implement keyless entry architectures that are equally or more vulnerable than their petrol equivalents. LockCar’s hardwired immobiliser adapts to EV electrical systems and provides the physical start-circuit defence that no factory EV security system currently delivers.
On this page
A widespread misconception among EV owners is that their vehicle is more secure than a petrol equivalent because it lacks a traditional ignition system and can often be managed via a smartphone app. The reality is more nuanced and more concerning. Electric vehicles — including Tesla, BMW i-series, Kia, Hyundai, and Volkswagen ID. models — use passive keyless entry systems that are fully vulnerable to relay attack. LockCar manufactures hardwired immobilisers compatible with EV high-voltage management systems, providing physical start-circuit protection for the UK’s growing population of electric vehicle owners.
The myth that EVs can’t be stolen
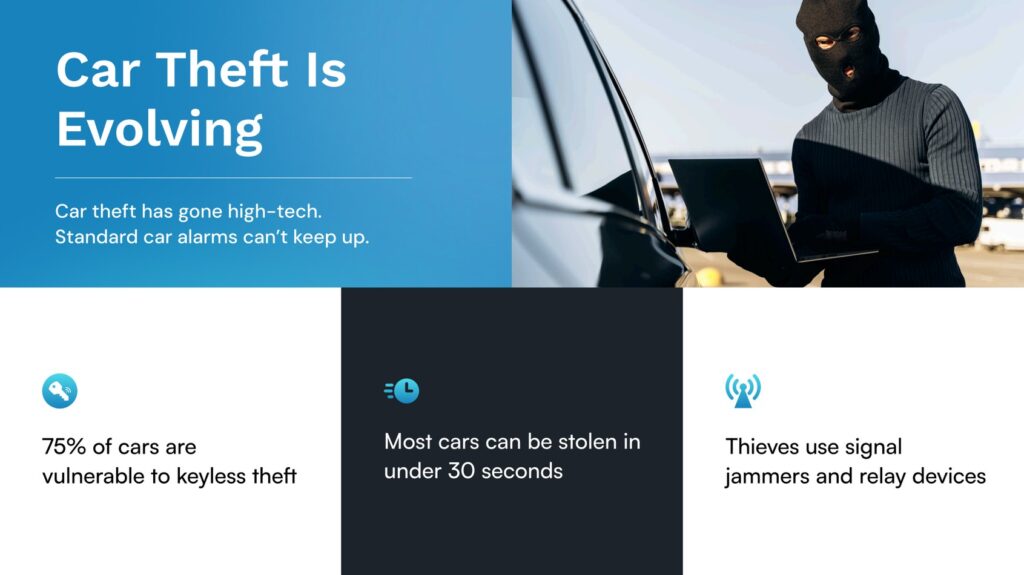
The belief that electric vehicles are harder to steal than petrol cars stems from two intuitions: that without a combustion engine there is nothing to “hot-wire,” and that the ability to remotely track or disable an EV via its manufacturer’s app provides meaningful security. Both intuitions are partially correct but fundamentally misleading when applied to the threat of relay attack.
Modern EVs do not need to be hot-wired — they use keyless entry and push-button start with the exact same passive radio-frequency architecture as keyless petrol vehicles. A relay attack on a BMW iX or a Kia EV6 works identically to a relay attack on a BMW X5 or a petrol Kia Sportage. The criminal extends the key fob’s signal, the vehicle receives a valid handshake, and the drive circuit engages. The absence of an ignition barrel is irrelevant — the attack bypasses the authentication mechanism that the ignition system depends on.
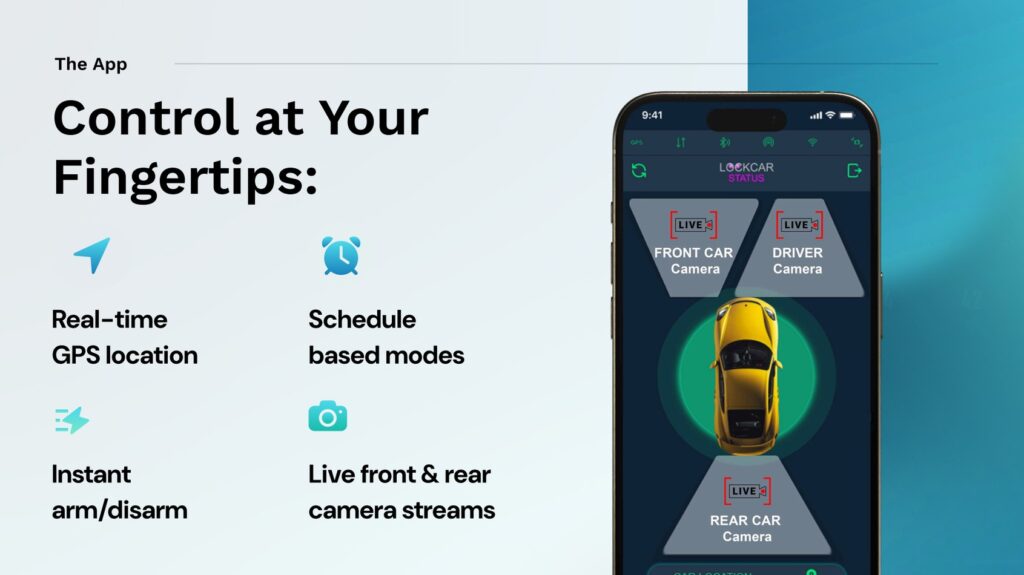
Manufacturer app security — such as Tesla’s app-based vehicle control — provides a useful layer of post-theft response but is not a prevention tool. A stolen Tesla can be tracked and potentially disabled remotely via the Tesla app, but this requires the owner to be awake and responsive, the cellular connection to remain active, and the criminal not to have taken the vehicle to a signal-blocking environment. These conditions cannot be guaranteed. A physical immobiliser that prevents the vehicle from moving in the first place eliminates all of these dependencies.
How EVs are stolen via relay attack
EV relay attacks follow the same operational sequence as petrol car relay attacks. The key fob — or in keycard-based systems, the keycard — broadcasts a continuous challenge-response signal. Relay equipment amplifies this signal from inside a property and retransmits it to the vehicle. The vehicle’s keyless entry system receives what appears to be a valid, proximate key signal and authorises drive engagement.
For Tesla vehicles, which use a smartphone app or NFC keycard rather than a traditional key fob, the relay attack vector is slightly different. Phone-as-key systems using Bluetooth Low Energy (BLE) are vulnerable to BLE relay attacks — a distinct but operationally similar technique where a criminal amplifies and retransmits the BLE handshake between the phone and the car. Criminalised BLE relay equipment has been documented in use against Tesla and other phone-as-key systems across Europe.
Once a relay attack has successfully engaged drive mode in an EV, the vehicle accelerates silently from the property — a characteristic that actually makes EV relay theft harder to detect than petrol car theft. There is no engine start sound, no exhaust noise. Neighbours and CCTV may not register the departure of a vehicle that pulls away silently at 2am.
Charging point risk — a new EV vulnerability
Public charging infrastructure has introduced a vehicle security risk scenario that has no parallel in petrol vehicle ownership. When an EV is left at a public charging point — particularly an overnight rapid charger at a motorway service station, a supermarket car park, or a workplace charging bay — the owner is not present with the vehicle. The key fob or phone may be inside a building, making relay attack possible if the charging location is surveilled by thieves.
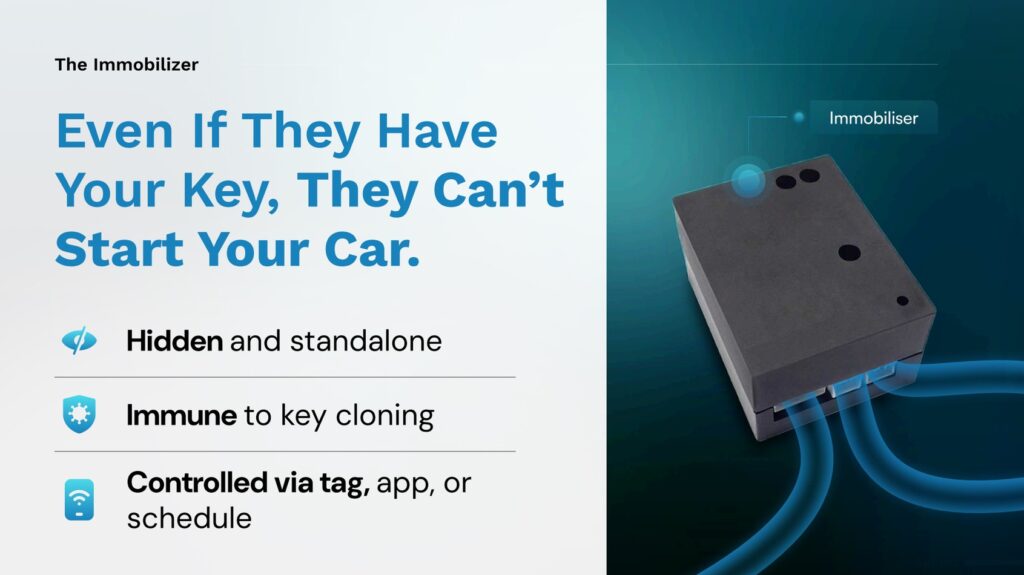
Supermarket and retail park charging bays are increasingly targeted for EV relay theft. Vehicles are left for 30 to 90 minutes while owners shop, and in many cases the key fob or phone travels inside the store with the owner, allowing a relay attack with the owner’s phone or fob just inside the building entrance. The LockCar immobiliser provides protection in exactly this scenario — even if a relay attack succeeds at a charging point, the drive circuit cannot engage without LockCar authentication.
Silent departure is a defining characteristic of EV relay theft that makes it harder to detect in progress. Neighbours, CCTV operators, and even the vehicle owner may not notice an EV being stolen because there is no engine noise. A LockCar immobiliser that prevents the drive circuit engaging is the most effective countermeasure for this specific scenario.
EV models most at risk in the UK
Tesla Model 3 and Model Y are the most commonly reported EV theft targets in the UK, reflecting their dominant market share and high residual values. BLE relay attack tools specifically designed for Tesla’s phone-as-key system have been documented in use across the UK and Europe. BMW i4, iX3, and iX models use Comfort Access — the same passive keyless system as BMW’s petrol range — and are equally vulnerable to standard relay attack equipment. Kia EV6 and EV9, Hyundai Ioniq 5 and Ioniq 6, and the Volkswagen ID.4 all use passive keyless entry and have appeared in EV theft reports as their UK registration numbers have grown.
Why app-based security isn’t enough
Manufacturer smartphone apps typically provide location tracking, remote locking, and in some cases remote disabling of a stolen vehicle. These capabilities are valuable but depend on a chain of conditions: the owner’s phone must be charged and connected to mobile data, the owner must receive and respond to an alert quickly, the vehicle must maintain a cellular connection, and the criminal must not have taken counter-measures against remote tracking.
Remote disable via app typically only works when the vehicle is stationary or moving below a set speed threshold — for safety reasons, manufacturers do not allow vehicles to be remotely disabled at motorway speed. This means a stolen vehicle must be stopped and then remotely disabled, rather than being stopped immediately. The window between theft completion and remote disable may be 10 to 30 minutes, potentially enough time to reach a Faraday-shielded storage location.
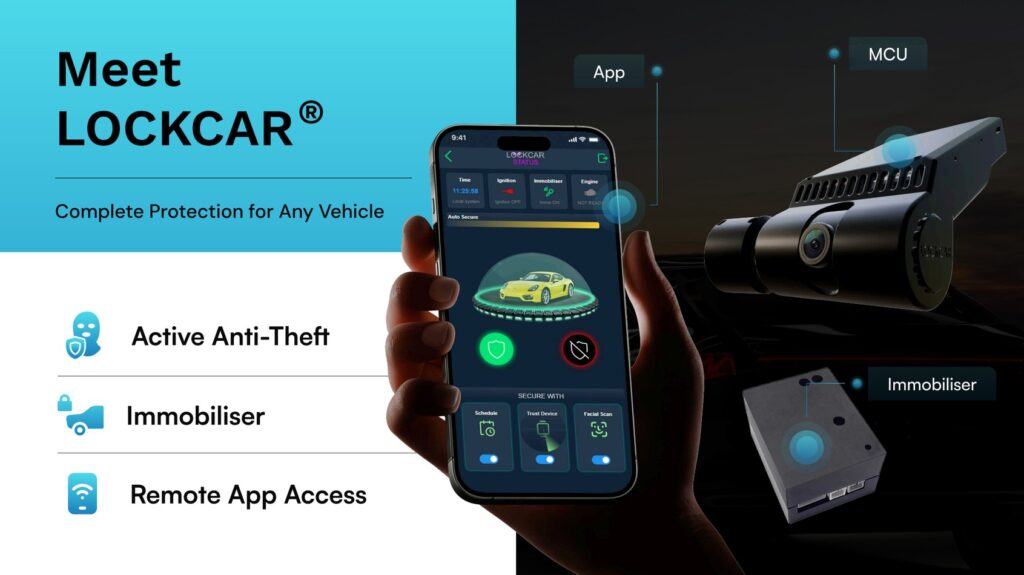
LockCar for electric vehicles
LockCar immobilisers adapt to EV electrical architectures. Rather than interrupting a traditional fuel pump or ignition circuit, LockCar’s EV installations integrate with the high-voltage drive engagement circuit — the point at which the inverter and motor receive authorisation to engage. The relay break at this point prevents the vehicle from entering drive mode regardless of whether the keyless entry system has been satisfied.
All LockCar installations on EV platforms use isolated, shielded wiring to ensure no interference with the vehicle’s BMS (Battery Management System), OBC (On-Board Charger), or high-voltage safety systems. Our engineers are trained in EV-specific installation procedures. The installation does not affect charging capability, regenerative braking, or any driver assistance features.
LockCar EV immobiliser range
Does LockCar work with Tesla’s phone-as-key system?
Yes. LockCar integrates with Tesla’s drive circuit independently of the phone-as-key, NFC keycard, or key fob systems. Even if a BLE relay attack satisfies Tesla’s keyless authentication, the LockCar relay break prevents drive mode from engaging. The two systems operate in parallel.
Will fitting LockCar affect my EV’s charging or battery management?
No. LockCar EV installations use shielded wiring procedures specifically designed to avoid any interaction with the BMS, OBC, or high-voltage system. Charging capability, regenerative braking, and all battery management functions are unaffected.
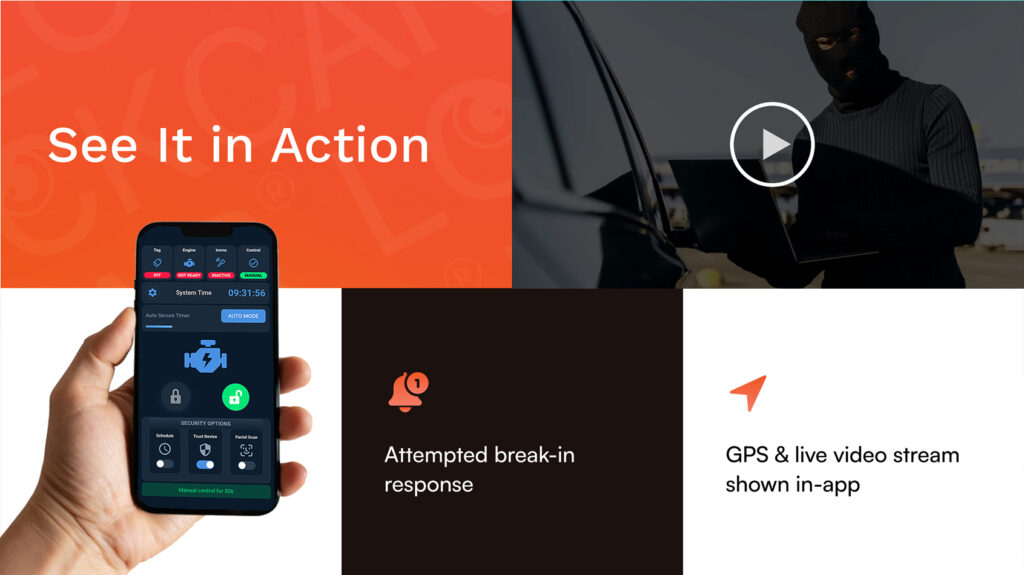
My EV’s manufacturer app already lets me track and disable it remotely — why do I need LockCar?
The manufacturer app provides reactive response after theft — it requires you to be awake, connected, and responsive. LockCar prevents the theft from completing in the first place, independently of your phone, internet connection, or reaction time. Prevention is always more reliable than response.
Book EV installation today
Tesla · BMW i · Kia · Hyundai · VW ID · All EV platforms · Mobile fitting
WhatsApp to book → Call VictorUK-wide